It's possible to use the Event Viewer on your local system to examine event logs on remote systems, provided you have permission to access those remote systems. To access the remote log files, start by displaying the Event Viewer. (The easiest way to do this is to use the search capabilities of Windows to look for "Event Viewer", without the quote marks.) (See Figure 1.)
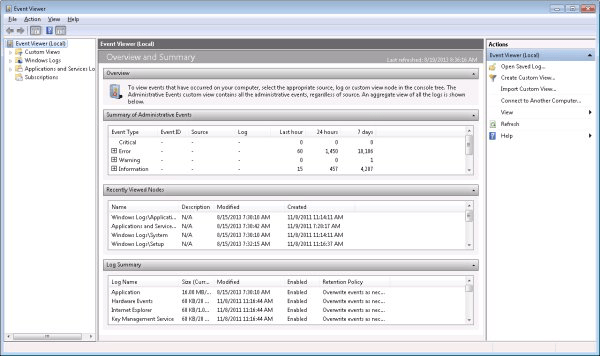
Figure 1. Event Viewer main screen.
To connect to another computer you can either use the menu (Action | Connect to another computer) or simply click the "Connect to Another Computer" link in the right pane of the main screen. Whichever way you do it, you are presented with the Select Computer dialog box. (See Figure 2.)
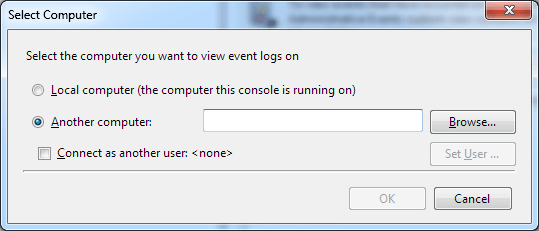
Figure 2. The Select Computer dialog box.
In the box to the right of the "Another Computer" wording you should either type in the name of the remote computer or click the Browse button to look for it. If you want to connect to the remote computer as a different user, click the checkbox labeled "Connect as Another User." If you do click the checkbox, you should then click the Set User button so that you can specify the credentials you want to use on the remote system. Clicking the Set User button displays a dialog box where you enter the user name and password of a user on the remote system.
When you are ready, click the OK button. The Event Viewer on the remote system appears, replacing the one currently on your screen. It is quite bare by comparison. (See Figure 3.)
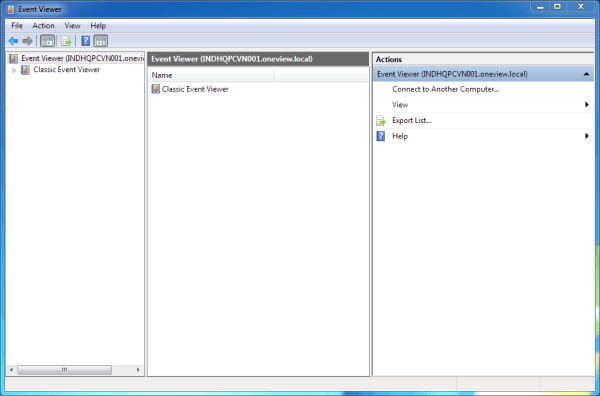
Figure 3. The Event Viewer on the remote computer.
You can now navigate through the remote Event Viewer just as you would navigate through the Event Viewer on your local machine. Start by clicking the "Classic Event Viewer" node in the left pane and following it to whatever logs you wish to look at. When you're finished, just close the window.
![]()
![]()
![]() This tip (12853) applies to Windows 7, 8, and 10.
This tip (12853) applies to Windows 7, 8, and 10.
By default, the event logs are implemented in a circular buffer, i.e., when its maximum size is reached, the oldest ...
Discover MoreThe Security event log captures success and failure audit events when auditing is turned on. This tip explains a bit more ...
Discover MoreThe System event log holds messages generated by device drivers. This tip explains more about it.
Discover MoreThere are currently no comments for this tip. (Be the first to leave your comment—just use the simple form above!)
Copyright © 2026 Sharon Parq Associates, Inc.
Comments